Define a subnet for Private Link Configuration
To enable Private Link Configuration, a subnet, different from the Application Gateway subnet, is required for the private link IP configuration. Private Link must use a subnet that doesn't contain any Application Gateways. Subnet sizing is determined by the number of connections required for your deployment. Each IP address allocated to this subnet ensures 64-K concurrent TCP connections that can be established via Private Link at single point in time. Allocate more IP addresses to allow more connections via Private Link. For example: n * 64K; where n is the number of IP addresses being provisioned.
Note
The maximum number of IP addresses per private link configuration is eight. Only dynamic allocation is supported.
Complete the following steps to create a new subnet:
Add, change, or delete a virtual network subnet
Configure Private Link
The Private link configuration defines the infrastructure used by Application Gateway to enable connections from Private Endpoints. While creating the Private Link configuration ensure a listener is actively utilizing the respected frontend IP configuration.Complete the following steps to create the Private Link configuration:
Go to the Azure portal
Search for and select Application Gateways.
Select the name of the application gateway you want to enable private link.
Select Private link
Configure the following items:
- Name: The name of the private link configuration.
- Private link subnet: The subnet IP addresses should be consumed from.
- Frontend IP Configuration: The frontend IP address that private link should forward traffic to on Application Gateway.
- Private IP address settings: specify at least one IP address
Select Add.
Within your Application Gateways properties blade, obtain and make a note of the Resource ID, this is required if you are setting up a Private Endpoint within a different Microsoft Entra tenant.
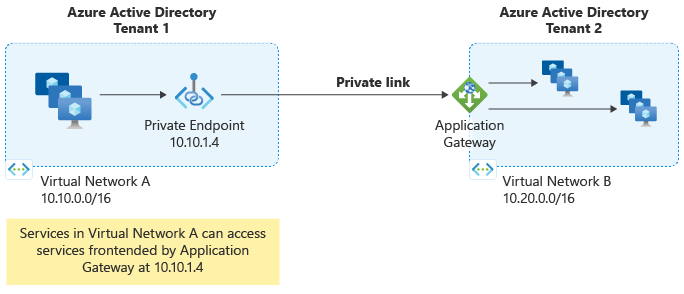
Configure Private Endpoint
A private endpoint is a network interface that uses a private IP address from the virtual network containing clients wishing to connect to your Application Gateway. Each of the clients uses the private IP address of the Private Endpoint to tunnel traffic to the Application Gateway. To create a private endpoint, complete the following steps:
- Select the Private endpoint connections tab.
- Select Create.
- On the Basics tab, configure a resource group, name, and region for the Private Endpoint. Select Next.
- On the Resource tab, select Next.
- On the Virtual Network tab, configure a virtual network and subnet where the private endpoint network interface should be provisioned to. Configure whether the private endpoint should have a dynamic or static IP address. Select Next.
- On the Tags tab, optionally configure resource tags. Select Next.
- Select Create.
Note
If the public or private IP configuration resource is missing when trying to select a Target sub-resource on the Resource tab of private endpoint creation, please ensure a listener is actively utilizing the respected frontend IP configuration. Frontend IP configurations without an associated listener won't be shown as a Target sub-resource.
Note
If you're provisioning a Private Endpoint from within another tenant, you will need to utilize the Azure Application Gateway Resource ID and the Name of the Frontend IP configuration as the target sub-resource. For example, if I had a private IP associated to the Application Gateway and the Name listed in Frontend IP configuration of the portal for the private IP is PrivateFrontendIp, the target sub-resource value would be: PrivateFrontendIp.
Note
If you have to move a Private Endpoint to another subscription, you must first delete the existing Private Endpoint connection between the Private Link and Private Endpoint. Once this is completed, you have to re-create a new Private Endpoint connection in the new subscription to establish connection between Private Link and Private Endpoint.
To configure Private link on an existing Application Gateway via Azure PowerShell, use following commands:
# Disable Private Link Service Network Policies
# https://zcusa.951200.xyz/azure/private-link/disable-private-endpoint-network-policy
$net =@{
Name = 'AppGW-PL-PSH'
ResourceGroupName = 'AppGW-PL-PSH-RG'
}
$vnet = Get-AzVirtualNetwork @net
($vnet | Select -ExpandProperty subnets | Where-Object {$_.Name -eq 'AppGW-PL-Subnet'}).PrivateLinkServiceNetworkPolicies = "Disabled"
$vnet | Set-AzVirtualNetwork
# Get Application Gateway Frontend IP Name
$agw = Get-AzApplicationGateway -Name AppGW-PL-PSH -ResourceGroupName AppGW-PL-PSH-RG
# List the names
$agw.FrontendIPConfigurations | Select Name
# Add a new Private Link configuration and associate it with an existing Frontend IP
$PrivateLinkIpConfiguration = New-AzApplicationGatewayPrivateLinkIpConfiguration `
-Name "ipConfig01" `
-Subnet ($vnet | Select -ExpandProperty subnets | Where-Object {$_.Name -eq 'AppGW-PL-Subnet'}) `
-Primary
# Add the Private Link configuration to the gateway configuration
Add-AzApplicationGatewayPrivateLinkConfiguration `
-ApplicationGateway $agw `
-Name "privateLinkConfig01" `
-IpConfiguration $PrivateLinkIpConfiguration
# Associate private link configuration to Frontend IP
$agwPip = ($agw | Select -ExpandProperty FrontendIpConfigurations| Where-Object {$_.Name -eq 'appGwPublicFrontendIp'}).PublicIPAddress.Id
$privateLinkConfiguration = ($agw | Select -ExpandProperty PrivateLinkConfigurations | Where-Object {$_.Name -eq 'privateLinkConfig01'}).Id
Set-AzApplicationGatewayFrontendIPConfig -ApplicationGateway $agw -Name "appGwPublicFrontendIp" -PublicIPAddressId $agwPip -PrivateLinkConfigurationId $privateLinkConfiguration
# Apply the change to the gateway
Set-AzApplicationGateway -ApplicationGateway $agw
# Disable Private Endpoint Network Policies
# https://zcusa.951200.xyz/azure/private-link/disable-private-endpoint-network-policy
$net =@{
Name = 'AppGW-PL-Endpoint-PSH-VNET'
ResourceGroupName = 'AppGW-PL-Endpoint-PSH-RG'
}
$vnet_plendpoint = Get-AzVirtualNetwork @net
($vnet_plendpoint | Select -ExpandProperty subnets | Where-Object {$_.Name -eq 'MySubnet'}).PrivateEndpointNetworkPolicies = "Disabled"
$vnet_plendpoint | Set-AzVirtualNetwork
# Create Private Link Endpoint - Group ID is the same as the frontend IP configuration
$privateEndpointConnection = New-AzPrivateLinkServiceConnection -Name "AppGW-PL-Connection" -PrivateLinkServiceId $agw.Id -GroupID "appGwPublicFrontendIp"
## Create private endpoint
New-AzPrivateEndpoint -Name "AppGWPrivateEndpoint" -ResourceGroupName $vnet_plendpoint.ResourceGroupName -Location $vnet_plendpoint.Location -Subnet ($vnet_plendpoint | Select -ExpandProperty subnets | Where-Object {$_.Name -eq 'MySubnet'}) -PrivateLinkServiceConnection $privateEndpointConnection
The following is a list of all Azure PowerShell references for Private Link Configuration on Application Gateway:
To configure Private link on an existing Application Gateway via Azure CLI, use following commands:
# Disable Private Link Service Network Policies
# https://zcusa.951200.xyz/azure/private-link/disable-private-endpoint-network-policy
az network vnet subnet update \
--name AppGW-PL-Subnet \
--vnet-name AppGW-PL-CLI-VNET \
--resource-group AppGW-PL-CLI-RG \
--disable-private-link-service-network-policies true
# Get Application Gateway Frontend IP Name
az network application-gateway frontend-ip list \
--gateway-name AppGW-PL-CLI \
--resource-group AppGW-PL-CLI-RG
# Add a new Private Link configuration and associate it with an existing Frontend IP
az network application-gateway private-link add \
--frontend-ip appGwPublicFrontendIp \
--name privateLinkConfig01 \
--subnet /subscriptions/XXXXXXXXXX-XXXX-XXXX-XXXX-XXXXXXXXXXX/resourceGroups/AppGW-PL-CLI-RG/providers/Microsoft.Network/virtualNetworks/AppGW-PL-CLI-VNET/subnets/AppGW-PL-Subnet \
--gateway-name AppGW-PL-CLI \
--resource-group AppGW-PL-CLI-RG
# Get Private Link resource ID
az network application-gateway private-link list \
--gateway-name AppGW-PL-CLI \
--resource-group AppGW-PL-CLI-RG
# Disable Private Endpoint Network Policies
# https://zcusa.951200.xyz/azure/private-link/disable-private-endpoint-network-policy
az network vnet subnet update \
--name MySubnet \
--vnet-name AppGW-PL-Endpoint-CLI-VNET \
--resource-group AppGW-PL-Endpoint-CLI-RG \
--disable-private-endpoint-network-policies true
# Create Private Link Endpoint - Group ID is the same as the frontend IP configuration
az network private-endpoint create \
--name AppGWPrivateEndpoint \
--resource-group AppGW-PL-Endpoint-CLI-RG \
--vnet-name AppGW-PL-Endpoint-CLI-VNET \
--subnet MySubnet \
--group-id appGwPublicFrontendIp \
--private-connection-resource-id /subscriptions/XXXXXXXXXX-XXXX-XXXX-XXXX-XXXXXXXXXXX/resourceGroups/AppGW-PL-CLI-RG/providers/Microsoft.Network/applicationGateways/AppGW-PL-CLI \
--connection-name AppGW-PL-Connection
A list of all Azure CLI references for Private Link Configuration on Application Gateway is available here: Azure CLI CLI - Private Link