Use the Azure Login action with a client secret
Learn how to create a service principal with a client secret and securely authenticate to Azure services from GitHub Actions workflows using Azure Login action.
In this tutorial, you learn how to:
- Create a GitHub secret for the service principal
- Set up Azure Login for service principal secret in GitHub Actions workflows
Warning
Treat your client secrets with care to prevent leaks. Unauthorized disclosure can compromise security. Store secrets securely and share only with authorized ones.
Prerequisites
- Create a Microsoft Entra application with a service principal by Azure portal, Azure CLI, or Azure PowerShell.
- Create a client secret for your service principal by Azure portal, Azure CLI, or Azure PowerShell.
- Copy the values for Client ID, Client Secret, Subscription ID, and Directory (tenant) ID to use later in your GitHub Actions workflow.
- Assign an appropriate role to your service principal by Azure portal, Azure CLI, or Azure PowerShell.
Create a GitHub secret for the service principal
Open your GitHub repository and go to Settings.

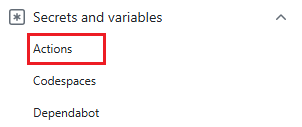
Select Security > Secrets and variables > Actions > New repository secret.
Note
To enhance workflow security in public repositories, use environment secrets instead of repository secrets. If the environment requires approval, a job cannot access environment secrets until one of the required reviewers approves it.
Create a GitHub Actions secret
AZURE_CREDENTIALSin the following format. Copy these values from your service principal.{ "clientId": "<Client ID>", "clientSecret": "<Client Secret>", "subscriptionId": "<Subscription ID>", "tenantId": "<Tenant ID>" }GitHub secret Service principal clientId Client ID clientSecret Client Secret subscriptionId Subscription ID tenantId Directory (tenant) ID
Set up Azure Login action with the Service Principal secret in GitHub Actions workflows
To authenticate to Azure in GitHub Actions workflows using the service principal secret, you need to use the Azure Login action.
Use the Azure Login action with both Azure CLI action and Azure PowerShell action
In this workflow, you authenticate using the Azure Login action with the service principal details stored in secrets.AZURE_CREDENTIALS. For more information about referencing GitHub secrets in a workflow file, see Using secrets in a workflow in GitHub Docs.
name: Run Azure Login with the Service Principal secret
on: [push]
jobs:
test:
runs-on: ubuntu-latest
steps:
- name: Azure Login action
uses: azure/login@v2
with:
creds: ${{ secrets.AZURE_CREDENTIALS }}
enable-AzPSSession: true
- name: Azure CLI script
uses: azure/cli@v2
with:
azcliversion: latest
inlineScript: |
az group show --name "<YOUR RESOURCE GROUP>"
# You can write your Azure CLI inline scripts here.
- name: Azure PowerShell action
uses: azure/powershell@v2
with:
azPSVersion: latest
inlineScript: |
Get-AzResourceGroup -Name "<YOUR RESOURCE GROUP>"
# You can write your Azure PowerShell inline scripts here.